New research from internet infrastructure giant Akamai shows that layer 7 (application layer) DDoS attacks have increased in volume while Layer 3 (network layer) and layer 4 (transport layer) attacks have increased in scale. These, together with increasing API and web application attacks have converged into a new operating model for attackers.
The latest State of the Internet Report from Akamai finds three major developments over the last year: DDoS attacks continue but evolve; API attacks increase, driven largely (but not solely) by growth in corporate use of agentic AI; and criminal use of AI as a force multiplier makes attacks cheaper, more sophisticated, stealthier and more difficult to attribute.
These are no longer singular attacks. Web app attacks, API abuse, bot activity and DDoS attacks appear as parts of the same campaign. “Convergence has shifted from an emerging trend to an operating model,” warns Brent Maynard, senior director for cybersecurity strategy at Akamai.
DDoS attacks
DDoS attacks continue to increase, both in quantity and effect. Over the last few years, the traditional layer 3 and layer 4 attacks have been joined by newer layer 7 attacks (which have increased by 104% over the last three years). The former floods the network and transport layers, ultimately disrupting company/customer interaction. The latter attacks APIs and web apps and are easier to launch via botnets and AI. They disrupt the victim’s operations, without necessarily causing visible downtime, making them difficult to detect.
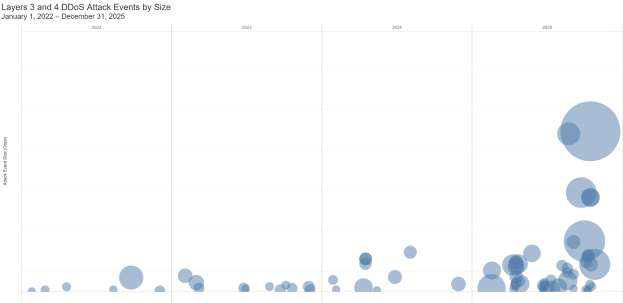
Layer 3 and layer 4 attacks have increased at a slower rate, but have achieved massive scale. Mirai remains the primary culprit but has been joined by variants and copycat botnets – some of which are offered as commercial DDoS for hire services.
Hacktivism remains the primary motivation, and with ongoing political tensions throughout EMEA, this is unlikely to stop. With the US/Iran conflict, it may grow in North America this year. However, we cannot ignore the possibility of inter-company rivalry and competition also being or becoming a separate motivation.
Convergence of attack capabilities can be seen in the appearance of both DDoS categories appearing in a single attack. Akamai pointed to “A customer that experienced a dynamic attack powered by a TurboMirai variant that shifted between Layers 3 and 4 and Layer 7.”
A different type of convergence is seen in Qilin, a Russia-linked RaaS group that has now reportedly added DDoS to its toolkit, and is currently the top ransomware threat targeting the US. “Qilin has updated its program and capabilities regularly,” reported Barracuda separately. “Throughout 2025, it has added spam campaigns, DDoS attack capabilities, automated network propagation, and automated ransom negotiation from within the affiliate panel.”
API attacks
APIs are among the most exposed entry points into the enterprise environment. Eighty-seven percent of companies experienced an API-related security incident in 2025. “APIs are now the prime targets of exploitation,” comments Akamai.
API attacks can also be used to increase the size of level 3 and 4 DDoS attacks. In June 2025, Akamai described, “how unsanitized JSON in API requests allowed attackers to run arbitrary commands, compromise exposed servers, and enroll them into DDoS‑capable botnets that receive instructions from remote command and control infrastructure to launch DDoS attacks.” Kaspersky blogged similarly around the same time.
API attacks are also one of the hardest to detect, especially courtesy of SaaS web apps. Web apps increasingly include agentic AI with multiple APIs. But in the haste to improve their products above the competition, SaaS can add agentic but omit to keep their customers fully cognizant; so, SaaS apps can simultaneously increase complexity and reduce visibility into the software being used. This is shadow AI. When the shadow AI includes undocumented APIs, it complicates and increases the existing shadow API problem.
This combination of increased use of APIs in SaaS apps together with the growth of API attacks in general has fueled an ongoing growth in web attack volume, up by 73% from the beginning of 2025 through the end of 2025. “Adversaries continuously probe enterprise environments, from customer-facing websites to back-end APIs, for exploitable security gaps that can lead to full-scale breaches,” reports Akamai.
“From an attacker’s perspective,” it writes, “for every web application there are APIs that expose functions and (potentially) data. The more vulnerable and easier the apps and APIs are to compromise, the quicker the threat actors can reach their objectives. The rise of AI agents that consume APIs to interact with the real world amplifies the problem.”
Steve Winterfeld, advisory CISO at Akamai, explains, “APIs are becoming more common. Companies are rapidly moving their infrastructure to APIs, and they’re also moving rapidly to AI. But as they do this, there are problems. Whenever you have transformation, you have difficulty with security. It’s just natural. So, you see API attacks up by 113% because that’s where the greatest return on investment for the attacker lives, along with the weakest security.”
“As a CISO,” says Winterfeld, “this report highlights the need for me to review my risk portfolio. Is my API program solid? Do I know what the business is doing with AI? Have I validated that my DDoS protections can handle the latest and greatest of these, including the layer 7 attacks that degrade my performance rather than stop my operation? Can I handle these new huge areas?”
The whole report is a testament to the need for security itself to converge. Just as, for attackers, “Convergence has shifted from an emerging trend to an operating model” by combining and blending web app attacks, API abuse, bot activity and DDoS attacks, so too must defenders converge their resources. It is no longer sufficient to have one team concentrating on API security, another focused on genAI and LLMs, and another concentrating on web attacks – they need to converge and integrate to maximize protection against this new attack operating model.
Related: Aisuru Botnet Powers Record DDoS Attack Peaking at 29 Tbps
Related: TurboMirai-Class ‘Aisuru’ Botnet Blamed for 20+ Tbps DDoS Attacks
Related: API Threats Grow in Scale as AI Expands the Blast Radius
Related: Cyber Insights 2026: API Security – Harder to Secure, Impossible to Ignore

