Despite years of security awareness efforts, an analysis of 6 billion credentials leaked in 2025 confirms that poor password hygiene persists, as simple numeric sequences and common words remain the primary choice for millions of users.
The data comes from a report published by password management firm Specops Software based on an analysis conducted by the threat intelligence team of its parent company, Outpost24.
The analysis found that the five most common passwords compromised in 2025 were ‘123456’, ‘123456789’, ‘12345678’, ‘admin’, and ‘password’.
For many years these passwords have been named as the most common credentials and the latest data indicates little change in user behavior.
While passwords such as ‘123456’ are typically used for personal accounts, ‘admin’ and ‘password’ are often default credentials for networking equipment, IoT devices, and industrial control systems (ICS) used in enterprise environments.
The failure to change these credentials can enable access to critical systems and have significant implications for an organization.
“In enterprise environments, this creates a real risk that malware-stolen credentials are reused as Active Directory (AD), virtual private network (VPN), or cloud identity passwords, giving attackers trusted access to corporate systems,” Specops said in its report.
Many of the analyzed passwords were slightly more complex than ‘123456’ and ‘admin’, but still contained predictable base terms such as ‘admin’, ‘guest’, ‘qwerty’, ‘secret’, ‘Welcome’, ‘student’, ‘hello’, and ‘password’.
“The repeated appearance of terms such as password and hello suggests operational rather than personal use. Analysis of the 500 most frequently recovered passwords shows a clear bias toward functional credentials tied to infrastructure, VPNs, and internal services, including variations of admin, root, and user,” Specops said.
The company has also observed regional and language-linked patterns in the compromised passwords, including ‘Pakistan123’ and ‘hola1234’. Name-based patterns have also emerged, with examples including ‘Kumar@123’ and ‘Rohit@123’.
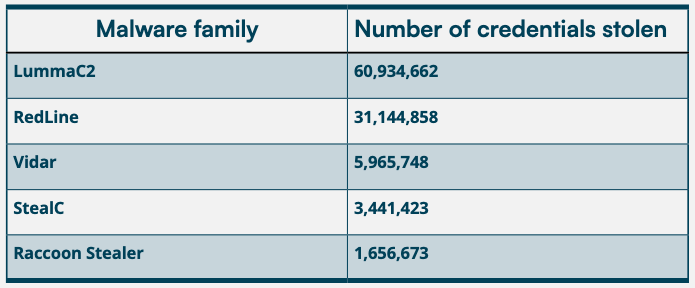
Many of these compromised passwords were stolen by malware, and the most active (based on the number of stolen credentials) was Lumma, followed by RedLine.
Specops pointed out that even in organizations that have adopted phishing-resistant and passwordless authentication passwords are likely still used for legacy systems, service accounts, and directory-based authentication.
The security firm recommends a layered defense that involves continuous monitoring of compromised credentials, the blocking of predictable patterns at creation, and the enforcement of phishing-resistant MFA and strong identity verification across all high-risk access paths and recovery workflows.
Related: Instagram Fixes Password Reset Vulnerability Amid User Data Leak
Related: Feds Seize Password Database Used in Massive Bank Account Takeover Scheme
Related: SonicWall Prompts Password Resets After Hackers Obtain Firewall Configurations

