An ongoing campaign, probably originating from a Russian-speaking threat actor, uses social engineering to trick victims into downloading an ISO file from cloud storage services such as Dropbox. Once mounted, the ISO file seems to be a legitimate part of the system and can be directly accessed by the victim. Opening a file within it will trigger a chain that downloads malware, including a module that discovering firm Aryaka has dubbed BlackSanta.
“BlackSanta, a dedicated BYOVD-based component, disables antivirus and EDR protections at the kernel level, clearing the path for credential harvesting, system reconnaissance, and eventual data exfiltration with minimal resistance,” warns Aditya Sood, Aryaka’s VP of security engineering and AI strategy.
Aryaka’s report on its findings explains how the campaign targets the generally trusted and less secured workflow of HR hirings. (There would, however, be little to prevent the attacker adapting components of the attack for other campaigns.)
This campaign targets hiring because HR is accustomed to, and routinely opens, attachments – an apparent resume found in the ISO appears to be legitimate and already on site.
Aryaka has no proof on how the victim is persuaded to download the malicious ISO file but assumes spear phishing. If the spear phishing target is in HR, that person would be unsurprised to find what appears to be an expected resume within the mounted ISO file – and would be more likely to open it.
The Aryaka report provides a sample ISO and explains how it delivers its malware.
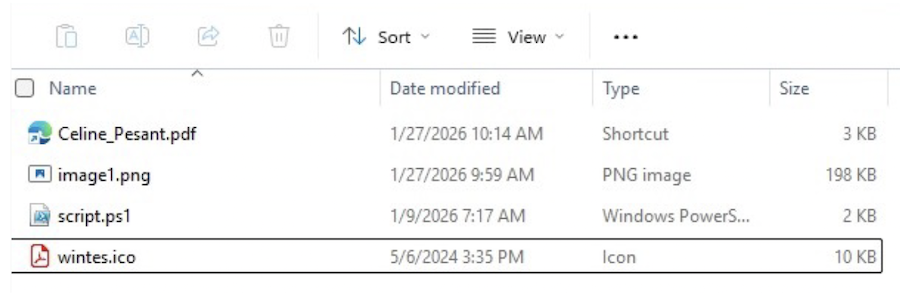
In this sample, the ISO contains four innocuous looking files. A security analyst might be instantly suspicious of a 3kb PDF file and the presence of a PowerShell script, but HR might simply not notice.
The PDF is a link file that launches cmd.com. “It executes an obfuscated command that dynamically constructs and launches powershell.exe with hidden window settings and execution policy bypass enabled,” notes the report. It ultimately runs script.ps1 from within the mounted ISO.
The script copies the PNG file to a separate location, loads it, and extracts hidden data from the image using least significant bit (LSB) steganography. This is decoded into a UTF-8 string representing a PowerShell which is executed in memory using Invoke-Expression.
The new script downloads SumatraPDF.zip from an external domain, It extracts this into a temporary folder. The ZIP contains two files: SumatraPDF.exe and DWrite.dll. The script runs the EXE, which loads the DLL (a tampered version of the legitimate DLL) that is accepted as genuine.
Once side-loaded, this tampered DLL collects basic system information, and user and host context by reading the USERNAME and COMPUTERNAME environment variables. Together, they provide the attacker with a single fingerprint string providing system and user context.
Further payloads are delivered by the C2. It prepares the environment: exits if it recognizes a Russian or CIS locale or language, exits if it finds a debugger, introduces noise and delays if it finds a sandbox, and modifies the registry keys for Windows Defender.
It then injects BlackSanta (a name found in its code), which Aryaka describes as a dedicated BYOVD-based component. “BlackSanta enumerates running processes, comparing each name against a hardcoded list of antivirus and EDR executables. When a match is found, it retrieves the process ID and uses its loaded drivers to unlock and terminate the targeted process at the kernel level, bypassing standard protections,” reports Aryaka.
Sood describes BlackSanta as the campaign’s most alarming feature. “It disables antivirus and EDR protections at the kernel level, clearing the path for credential harvesting, system reconnaissance, and eventual data exfiltration with minimal resistance,” he says.
Aryaka has found evidence that the campaign has been operational for a year, largely unnoticed, harvesting data and cryptocurrency artifacts. “It is not opportunistic malware,” says Sood. “It is operationally disciplined intrusion engineering. This operation reflects a mature adversary capable of blending social engineering, living-off-the-land techniques, steganography, and kernel-level abuse to achieve stealthy persistence and credential theft.”
Related: ClickFix Attack Uses Windows Terminal to Evade Detection
Related: Nation-State iOS Exploit Kit ‘Coruna’ Found Powering Global Attacks
Related: RATs in the Machine: Inside a Pakistan-Linked Three-Pronged Cyber Assault on India

