Cybersecurity analysts are closely monitoring the threat landscape following joint US-Israeli strikes against Iran. Security firms report that while hacktivist attacks have spiked, Iranian state-sponsored actors remain notably quiet.
The conflict began on February 28, 2026, with US and Israeli airstrikes hitting targets throughout Iran, including military bases, missile production sites, nuclear-related facilities, and senior leadership positions.
The attacks, conducted as part of Operation Epic Fury (US) and Operation Roaring Lion (Israel), resulted in the deaths of Supreme Leader Ayatollah Ali Khamenei and other high-ranking figures.
Iran retaliated by firing large numbers of missiles and drones at US military installations across the Persian Gulf region and launching direct strikes against Israel. Iran’s response has resulted in fatalities and damage across military and civilian targets, but the impact appears relatively minor.
The cyber operations conducted by the US and Israel alongside kinetic attacks appeared highly targeted and they reportedly had a significant impact.
According to media reports, the cyberattacks severely disrupted Iranian systems, targeting state media outlets like IRNA, IRGC communications and command networks, government digital services, and key infrastructure in the energy and aviation sectors. Pro-Western hackers also compromised a widely used prayer app to broadcast messages signaling external intervention.
General Dan Caine, chairman of the Joint Chiefs of Staff, said in a press briefing at the Pentagon on Monday that “coordinated space and cyber operations effectively disrupted communications and sensor networks across the area of responsibility, leaving the adversary without the ability to see, coordinate, or respond effectively.”
Iranian attacks observed by the cybersecurity industry
Several major cybersecurity firms have shared information about what they have observed in recent days on the cyber front of the conflict, particularly operations conducted by Iranian and pro-Iran hackers.
CrowdStrike reported on March 2 that it had not detected any large-scale cyber campaigns conducted by state-sponsored actors. However, the security firm has seen a surge in hacktivist attacks by pro-Iran groups, including website defacements, DDoS attacks, and claims of interference. The company highlighted Hydro Kitten, a group that claims to be targeting the financial sector.
“At this stage, much of the activity being publicized appears to be claim-driven rather than evidence-backed,” explained Adam Meyers, head of counter adversary operations at CrowdStrike. “It’s common during periods of geopolitical escalation to see an increase in opportunistic hacktivism and low-level disruptive activity designed to generate attention.”
Palo Alto Networks also saw an escalation in attacks conducted by hacktivists from outside Iran, but pointed out that state-sponsored hacking has not surged, likely due to limited internet connectivity resulting from the ongoing blackout, which at the time of writing has entered its fourth day.
“State-aligned cyber units may be acting in operational isolation, which could result in deviations from previously established patterns. Additionally, Iranian command and control degradation may also lead to tactical autonomy for cells outside of Iran. However, the capacity to sustain sophisticated cyber operations is likely reduced due to the operational disruptions.
For Iran-aligned threat actors based outside of the region, we assess that hacktivist groups will target organizations perceived as adversaries but their impact is likely to be of low to medium significance. Other nation-state-aligned threat actors may attempt to exploit the situation to activate cyberattacks to further their own interests.”
Threat intelligence company Flashpoint told SecurityWeek that hackers have made “alarming claims” about intrusions into industrial control systems (ICS) and national grain supply logistics.
Flashpoint reported that a broad coalition of pro-Iran and pro-Russia groups launched OpIsrael, a campaign focusing on data exfiltration and critical infrastructure attacks.
The group NoName057(16) has launched massive DDoS attacks against an Israeli defense contractor and municipal governments. The Cyber Islamic Resistance group claimed to have hacked the systems of an Israeli health insurance provider, while FAD Team has conducted SQL injection attacks to steal data, including from a virtual US Air Force group and educational institutions in France, India, and Vietnam. FAD is also alleged to have taken control of firewall monitoring dashboards in Saudi Arabia.
A group called Fatimion Cyber Team has targeted Arab states perceived as US allies, disabling the Bahrain News Agency and launching DDoS attacks against Qatari oil firm Gasco and Qatar Radio.
Cisco Talos has also been monitoring the US-Israel-Iran cyberattacks and reported on Monday that it had not seen any significant impacts.
“Currently there does not appear to be any significant increase in cyber activity associated with state-sponsored or state-affiliated groups,” Talos said.
It added, “Any possible impacts will likely be from sympathetic groups like hacktivists, some of whom have already launched website defacement and DDoS campaigns in support of Iran. Additionally, cyber criminals are likely to take advantage of the war to try and increase their scope of infections through the use of lures and other social engineering avenues.”
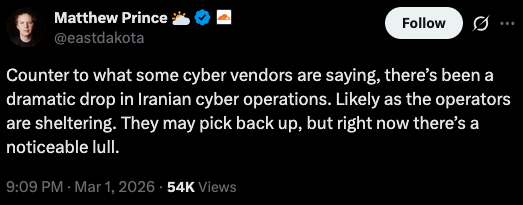
Sophos said on March 2 that it has seen “a surge in hacktivist activity, but not an escalation in risk, across Telegram, X, and underground forums following the February 28 strikes, primarily from pro-Iran personas including Handala Hack team and APTIran.”
The company has observed DDoS attacks and website defacements, noting that claims of critical infrastructure compromise made by hacktivists have not been verified and may be exaggerated.
While security firms have not seen any escalation in activity conducted by Iranian state-sponsored groups, Check Point reported that some government actors, such as Cotton Sandstorm (aka Emennet Pasargad) and Void Manticore (Handala), have reactivated old hacktivist personas, claiming to have hacked websites and infrastructure.
Hudson Rock, a company specializing in infostealer malware intelligence, reported that many of the data breaches claimed by hackers in recent days are fake.
While some reports of cyber disruptions or damage may turn out to be overstated, the fact that state-linked actors can carry out sophisticated intrusions alongside physical military operations highlights a real and growing threat that calls for ongoing vigilance and strong defenses.
The UK’s National Cyber Security Centre (NCSC) said that while “there is likely no current significant change in the direct cyber threat from Iran to the UK”, it urged organizations in the country to review their risk posture and take action.
Related: Cyber Insights 2026: Cyberwar and Rising Nation State Threats
Related: US Braces for Cyberattacks After Bombing Iranian Nuclear Sites

