Google on Monday published the M-Trends 2026 report, which is based on information collected by its Threat Intelligence Group and insights from more than 500,000 hours of incident investigations conducted by Mandiant in 2025.
One of the most notable findings of the industry benchmark report is that the time between initial access to an organization’s systems and the handoff to a secondary threat group has decreased from hours to seconds over the past few years.
In 2022, the median time between initial access and the handoff exceeded 8 hours, but it has steadily decreased since 2023, reaching only 22 seconds in 2025.
Mandiant researchers believe this indicates a “closer collaboration between initial access partners and secondary groups”.
They also noted that in many cases the short time window can be the result of an automated process where initial access brokers deliver malware directly on behalf of the secondary groups rather than advertising the obtained access on cybercrime forums.
The most common initial infection vector, accounting for 32% of cases, was exploits, followed by phishing (11%), prior compromise (10%), and stolen credentials (9%). Email phishing only accounted for 6% of the total, with this vector seeing a significant decline in recent years, down from 22% in 2022.
The three vulnerabilities that were most often exploited for access were the SAP NetWeaver vulnerability CVE-2025-31324, the Oracle EBS flaw CVE-2025-61882, and the SharePoint flaw CVE-2025-53770 (ToolShell).
Breaches were detected internally in 52% of cases, and victims learned about the intrusion from an external entity in 34% of cases.
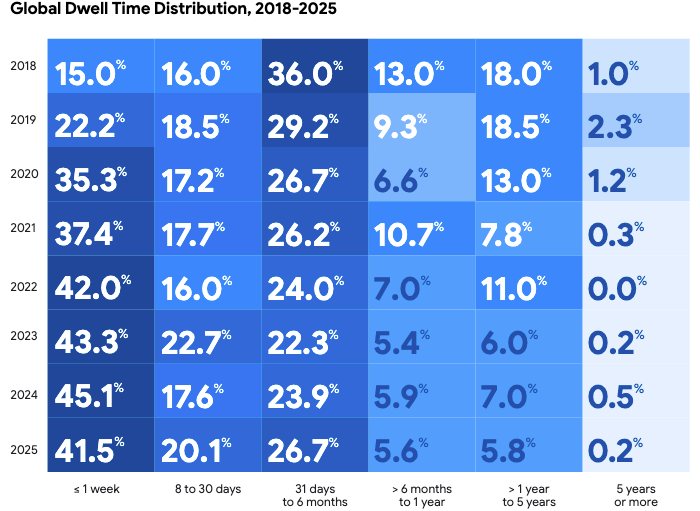
As for the dwell time, the number of days an attacker is present in the victim’s environment before being detected, the median was 14 days in 2025, a slight increase from 10 days in 2023 and 11 days in 2024. However, over the past decade the number has dropped significantly, from 146 in 2015.
Mandiant has seen an increase in incidents that remained undetected for 1-6 months, which appears to be the result of North Korean IT workers and cyberespionage actors, who go to great lengths to evade detection.
Roughly 30% of the attacks observed in 2025 were motivated by financial gain, and 40% of all incidents involved data theft.
The most targeted sector in 2025 was high-tech, followed by financial, business services, and healthcare.
As for malware, Google’s Threat Intelligence Group identified 714 new families last year, up from 632 in 2024. Of the new malware spotted in 2025, 146 targeted Linux and 55 targeted macOS.
The malware family most frequently observed in 2025 was GoldVein, the downloader used by the Cl0p cybercrime group in the Oracle EBS campaign, followed by the Akira ransomware.
Mandiant has also investigated cloud-related compromises and found that voice phishing was the most common initial vector, largely driven by ShinyHunters and Scattered Spider activity. Voice phishing accounted for 23% of intrusions, followed by third-party compromise (17%), stolen credentials (16%), email phishing (15%), and insider threats (14%). Exploits only accounted for 6% of cloud attacks.
The full M-Trends report also covers regional trends.
Related: Hacktivists, State Actors, Cybercriminals Target Global Defense Industry, Google Warns
Related: Google: Half of 2025’s 90 Exploited Zero-Days Aimed at Enterprises
Related: SecurityWeek Report: 426 Cybersecurity M&A Deals Announced in 2025

