Microsoft has silently mitigated an exploited LNK vulnerability with its November 2025 security updates, Acros Security says.
Tracked as CVE-2025-9491 (CVSS score of 7.0), the security defect allowed threat actors to obfuscate the purpose of malicious LNK files by hiding code from the user’s view.
The bug was disclosed in March by Trend Micro’s Zero Day Initiative (ZDI), which warned that nearly a dozen threat actors had been exploiting it for years. In October, exploitation was still ongoing.
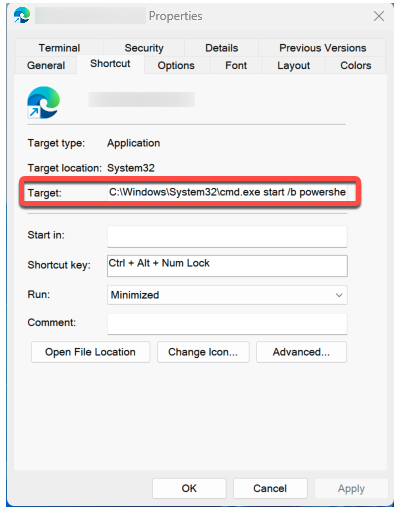
ZDI explained that Windows failed to display critical information that could surface malicious activity when the user inspected the properties tab of a shortcut (LNK) file.
Thus, threat actors have been using specially crafted LNK files embedding command-line arguments leading to malware execution.
As successful exploitation requires that the user manually execute the shortcut file, the attackers have been disguising them as harmless documents.
The issue was that, when displaying a LNK file’s properties, Windows only showed the first 260 characters in the ‘Target’ field, although the file’s structure theoretically allows for strings of up to 32k characters.
Windows would simply cut off the rest of the string, essentially hiding from users’ view extremely long PowerShell or BAT scripts, notes Acros Security.
And with threat actors using whitespaces for the first 260 characters in the string, the entire command was completely hidden from users who would take their time to glance over the file’s properties.
User interaction is key to exploitation
In fact, Microsoft previously told SecurityWeek, users typically do not inspect a file’s properties, and Microsoft Defender has detections to recognize the technique.
Saying that the vulnerability did not meet the bar for immediate servicing, the company explained it was considering addressing it in a feature release.
According to Acros Security, Microsoft’s November security updates have resolved the exploited LNK vulnerability, as Windows now displays the entire string in the ‘Target’ field in a shortcut file’s properties tab.
Acros Security has developed an alternative patch for users of its 0Patch solution.
On November 1, Microsoft published guidance on CVE-2025-9491, underlining that existing protections in Windows, coupled with warnings when downloading files from the internet and the necessary user interaction to open LNK files, mitigate the threat.
LNK files, it explains, can be delivered only within ZIP archives that users need to open. Furthermore, when opening such a shortcut file, Windows warns the user that the format is not trusted.
“Windows identifies shortcut files (.lnk) as a potentially dangerous file type. Attempting to open a .lnk file downloaded from the Internet automatically triggers a security warning advising users not to open files from unknown sources, and we strongly recommend heeding this warning,” Microsoft’s guidance reads.
Update: Acros Security has updated its initial blog to point out that the vulnerability was likely addressed in mid-2025.
“A friend in the know subsequently pointed out that this change had been deployed by Microsoft already in June 2025 but it may have been activated gradually. For instance, one of our testing Windows 11 24H2 computers we re-inspected had it activated in August. Our claim that it was deployed in November was therefore incorrect.”
*Updated with additional information from Acros Security and the link to Microsoft’s advisory on CVE-2025-9491.
Related: Chrome 143 Patches High-Severity Vulnerabilities
Related: Over 50,000 Asus Routers Hacked in ‘Operation WrtHug’
Related: Data Exposure Vulnerability Found in Deep Learning Tool Keras
Related: Vulnerability in OpenAI Coding Agent Could Facilitate Attacks on Developers

