A new Android malware named Albiriox is being offered on cybercrime forums by Russian-speaking threat actors, according to online fraud management company Cleafy.
Albiriox is a banking trojan designed for on-device fraud (ODF), enabling attackers to take control of compromised mobile devices to carry out fraudulent transactions from the victim’s cryptocurrency or banking applications.
The malware appears to be under development. It includes remote access functionality that enables real-time control of the compromised Android device, a feature that seems fully operational.
Albiriox can also be used for overlay attacks, which involve displaying phishing pages on top of legitimate applications to trick users into handing over their banking and cryptocurrency credentials. This functionality was still under development when Cleafy researchers analyzed the malware.
Albiriox emerged in September, when its developers started recruiting users for an early version. The trojan has been offered under a malware-as-a-service (MaaS) model since October, at a price of $650 per month for those who bought a subscription in the first week, and $720 per month starting on October 21.
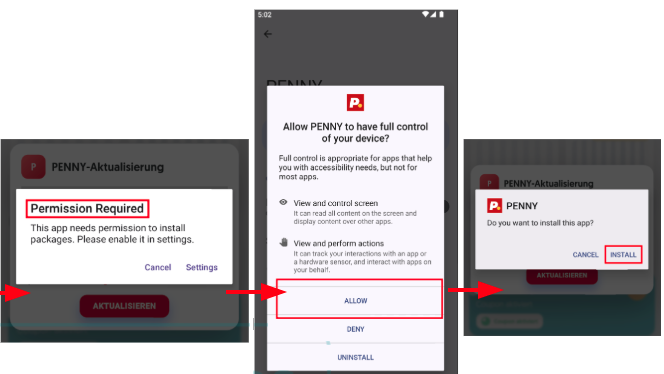
One of the first Albiriox campaigns targeted users in Austria, tricking them into installing the malware by advertising a fake app for the Penny supermarket.
This fake app served as a dropper designed to trick the victim into granting elevated permissions and then delivering the Albiriox malware itself as the final payload.
An analysis of the malware revealed that it targets more than 400 applications worldwide, including banking, crypto, fintech, wallet, trading, payments, investment, and gaming apps.
In order to increase the malware’s chances of evading detection, its developers provide a custom builder that integrates with a crypting service named Golden Crypt.
“The inclusion of Golden Crypt within the builder pipeline suggests that the Albiriox operators are deliberately positioning the malware as a stealth-optimized product, aiming to evade static detection mechanisms and improve the likelihood of successful deployment during the early infection stages, especially relevant given the malware’s reliance on the two-stage delivery and accessibility-based device takeover,” Cleafy researchers explained.
UPDATE: Google provided the following statement to SecurityWeek:
“Google confirmed that users are protected against known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services.”
Related: New Sturnus Banking Trojan Targets WhatsApp, Telegram, Signal Messages
Related: Chinese Cyberspies Deploy ‘BadAudio’ Malware via Supply Chain Attacks
Related: Landfall Android Spyware Targeted Samsung Phones via Zero-Day

