ZeroDayRAT is a new commercial mobile spyware toolkit that enables full remote access to Android and iOS devices, with features including live camera feeds, key logging, bank and crypto theft and more.
It is currently available via Telegram, and was first observed on February 2, 2026, and since analyzed by iVerify. It is “a complete mobile compromise toolkit” comparable to kits normally requniring nation-state resources to develop.
Infection requires delivery of a malicious binary. “These kits typically give the buyer a self-hosted panel and a builder,” explains Daniel Kelley, research fellow at iVerify. “The operator sets up their own server, configures the panel, then uses the builder to generate payloads that phone home to their infrastructure.”
From there, he continues, “Distribution is on the attacker: phishing links, smishing, trojanized apps on third-party stores, social engineering… whatever works. There’s an ‘exploit’ tab in the sidebar, so it’s possible it comes with some kind of exploit capability, but we can’t confirm it.”
Once installed on the target, capabilities include victim and device profiling (model, OS, battery, country, lock status, SIM and carrier info, dual SIM phone numbers, app usage broken down by time, a live activity timeline, and a preview of recent SMS messages).
Location tracking is also available. GPS coordinates are pulled and plotted on an embedded Google Maps with location history (where the victim is, and where the victim has been).
App usage is provided, including name and content: WhatsApp messages, Instagram notifications, missed calls, Telegram updates, YouTube alerts, system events… This goes deeper with details of registered accounts, providing Google, WhatsApp, Instagram, Facebook, Telegram, Amazon (and more) username and email – a complete and ready-made social engineering target source.
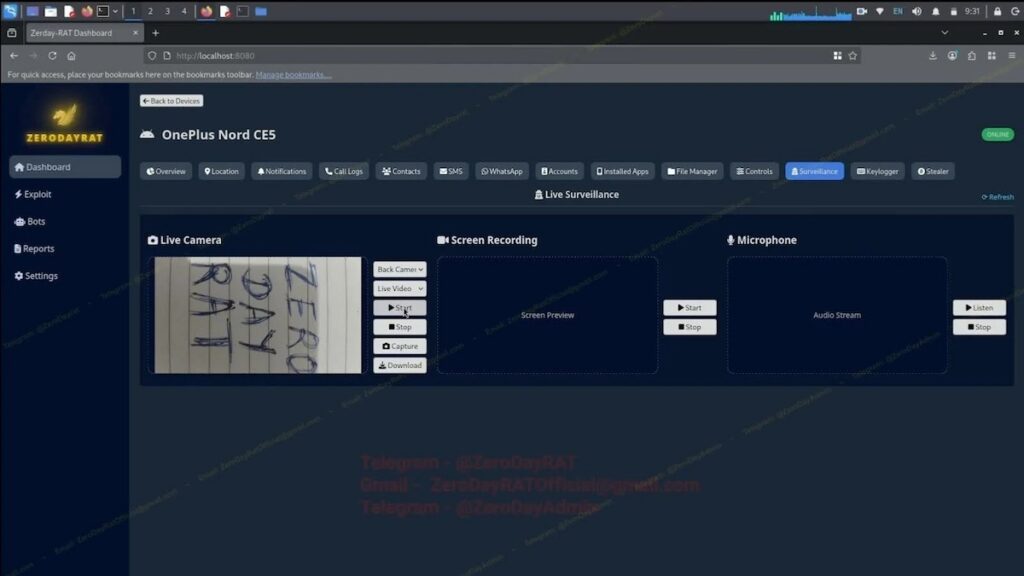
All of this is passive collection from the victim’s device; but the kit also provides live surveillance including live camera streaming (front or back), screen recording, and a microphone feed. “Combined with GPS tracking, an operator can watch, listen to, and locate a target simultaneously,” writes iVerify.
Mobile keylogger, crypto theft
A keylogger captures every input: biometric unlocks, gestures, keystrokes, and app launches. The attacker is able to see what the victim is doing and what is being typed simultaneously.
Capability also includes bank and crypto theft. There are few if any IoCs available. A shortened phone battery life is a flag, but not proof. Financial theft is probably the most visible flag.
“The crypto stealer runs clipboard injection continuously, so theft happens whenever the victim tries to send funds. Unexplained outbound transactions to addresses victims don’t recognize would be a red flag,” explains Kelley.
“The bank stealer goes after credentials rather than initiating transfers directly. There would be unauthorized logins. But by the time it shows up in financial records, the damage is done.”
With most RATs, discovery of presence often triggers a malware wipe. It’s not yet clear if this is available for ZeroDayRAT. Kelley comments, “Remote wipe is pretty standard in commercial RATs. It would be unusual for something this full featured not to have it. We’d call it plausible but unconfirmed.”
Takedown challenges
iVerify describes ZeroDayRAT as a problem that isn’t going away. Firstly, it is almost impossible to detect the creator (for potential arrest). The toolkit is advertised in five languages: Portuguese, Russian, Chinese, Spanish, and English.
“We’ve seen them post messages in Chinese, use a Russian domain, and target Indian victims,” says Kelley. “None of it lines up, and that looks intentional. We think they’re actively using disinformation to muddy attribution.”
Similarly, there is no central server for authorities to locate and take down. “Every operator runs their own instance, so you’re playing whack-a-mole against individual infrastructures. The Telegram sales channel is the most visible chokepoint, but Telegram takedowns are slow, and even if it happens the developers just spin up a new channel.”
This is a worrying new spyware RAT that may be with us for some time.
Related: Google Ships Android ‘Advanced Protection’ Mode to Thwart Surveillance Spyware
Related: Can ‘Lockdown Mode’ Solve Apple’s Mercenary Spyware Problem?
Related: Apple Adds ‘Lockdown Mode’ to Thwart .Gov Mercenary Spyware
Related: Apple Adds ‘BlastDoor’ to Secure iPhones From Zero-Click Attacks

