VPN company NordVPN has denied suffering a breach after a threat actor leaked data allegedly stolen from its systems.
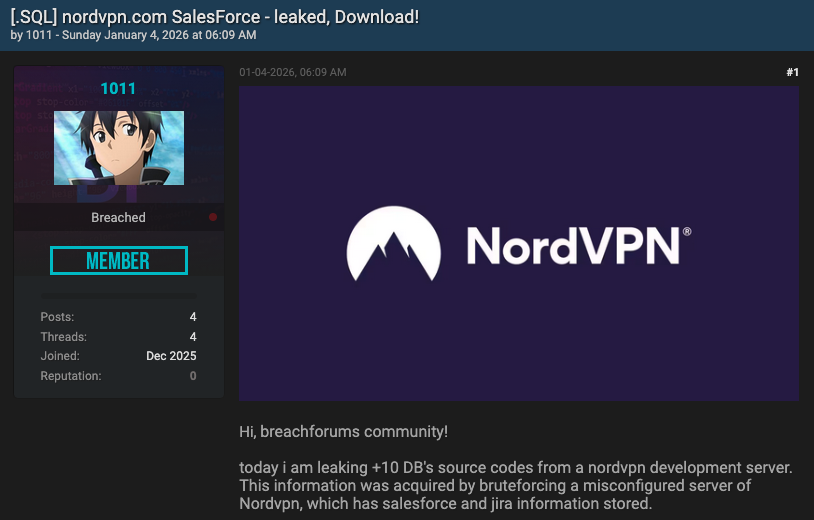
The hacker claimed on January 4 on the BreachForums cybercrime forum that they had obtained source code from a “NordVPN development server”.
“This information was acquired by bruteforcing a misconfigured server of NordVPN, which has Salesforce and Jira information stored,” the hacker said.
The attacker publicly released some sample data and made all the information available for download to the cybercrime forum’s premium users.
NordVPN responded to the claims on January 5, saying that while its probe is ongoing, an initial forensic analysis has not found any evidence of its servers or internal production infrastructure being compromised.
In addition, NordVPN clarified that the leaked data does not originate from its Salesforce environment or any other internal system. Instead, it appears to come from a third-party automated testing platform that the company evaluated six months ago.
The VPN firm said it ended up choosing the services of a different vendor, but during the trial period it did create a temporary environment to test the platform’s functionality.
However, the test environment was never connected to its production systems, and no real customer data, source code, or credentials were ever uploaded.
“The claims that our internal Salesforce development servers were breached are false. The leaked elements, such as the specific API tables and database schemas can only be artifacts of an isolated third-party test environment, containing only dummy data used for functionality checks,” NordVPN said.
“While no data in the dump points to NordVPN, we have contacted the vendor for additional information,” the company added.
Related: TorGuard, NordVPN Respond to Breach Reports
Related: Verizon DBIR Flags Major Patch Delays on VPNs, Edge Appliances
Related: New VPN Attack Demonstrated Against Palo Alto Networks, SonicWall Products

