North Korea has dramatically scaled digital operations to fund its sanctioned regime, according to data from Amazon and blockchain analysis firm Chainalysis.
A new report from Chainalysis reveals that North Korean hackers have stolen more than $2 billion worth of cryptocurrency in 2025, a significant increase from the roughly $1.3 billion recorded in 2024.
Complementing these heists is a pervasive network of fake IT workers, with Amazon reporting the detection and blocking of 1,800 North Korean IT workers attempting to secure high-paying remote roles through sophisticated identity fraud.
North Korea’s cryptocurrency heists
The report published on Thursday by Chainalysis shows that a total of $3.41 billion in cryptocurrency was stolen by hackers between January and early December 2025, a significant portion represented by the $1.5 billion Bybit heist. The 2025 total is only slightly higher than in 2024, when $3.38 billion was stolen.
Of the $3.41 billion, at least $2.02 billion worth of cryptocurrency is believed to have been stolen by North Korean hackers, who are also behind the Bybit hack.
“This marks the most severe year on record for DPRK crypto theft in terms of value stolen, with DPRK attacks also accounting for a record 76% of all service compromises,” Chainalysis said.
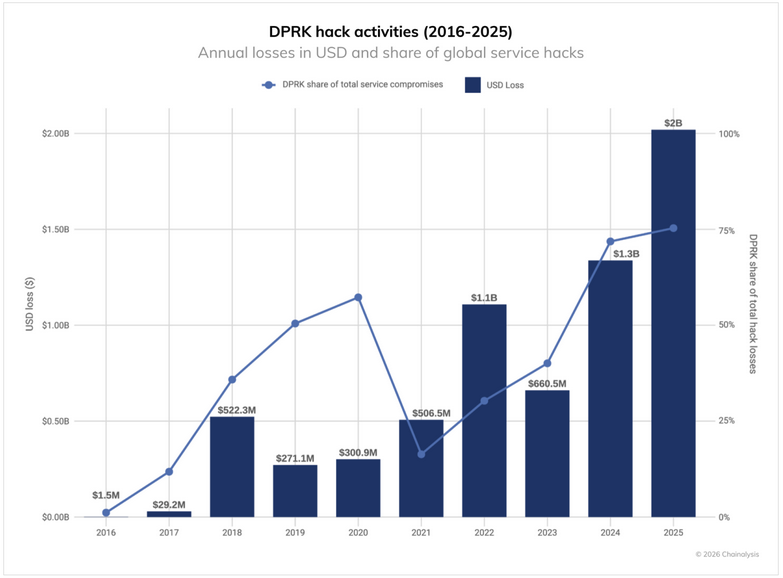
According to the company’s calculations, the all-time total amount of cryptocurrency stolen by North Korean threat actors has reached $6.75 billion.
Despite the record-breaking amount stolen in 2025, the actual frequency of attacks conducted by North Korean hackers has decreased, with Chainalysis noting that they have likely reduced their operational tempo in the wake of the Bybit attack to focus on laundering the stolen cryptocurrency.
Chainalysis pointed out that North Korea’s crypto theft operations are increasingly relying on its IT workers getting jobs at cryptocurrency exchanges, custodians, and Web3 companies, and serving as insiders.
In addition, North Korean threat actors are increasingly posing as recruiters, orchestrating fake hiring processes in an effort to collect credentials, source code, and other valuable information. They also pose as potential investors and acquirers to collect intelligence.
Amazon targeted by North Korean IT workers
The scale of the North Korean IT worker scheme is illustrated by data from Amazon. The tech giant’s chief security officer, Stephen Schmidt, said the company has identified more than 1,800 suspected North Koreans trying to get employment since April 2024, with a 27% quarter-over-quarter increase this year.
“Our AI model analyzes connections to nearly 200 high-risk institutions, anomalies across applications, and geographic inconsistencies,” Schmidt explained. “We verify identities through background checks, credential verification, and structured interviews.”
North Korean IT workers often rely on stolen identities and are aided by people in the United States, who host laptops provided by the victim company to make it appear as if the employee is located in the US.
Schmidt noted that their tactics are becoming increasingly sophisticated: they steal the identities of real software engineers, they hack LinkedIn accounts or pay for access to people’s accounts to boost their chances, and they are increasingly targeting AI-related roles due to their higher demand.
As for identifying these types of threats, the Amazon CSO recommends looking for small details, such as using ‘+1’ instead of ‘1’ for US phone numbers.
Inconsistencies in educational history also serve as critical indicators. Schmidt warned of candidates claiming degrees in majors not offered by their listed universities or providing graduation timelines that conflict with standard academic schedules.
Related: North Korea’s Fake Recruiters Feed Stolen Data to IT Workers

