LAS VEGAS — BLACK HAT USA 2024 — An analysis conducted by internet intelligence platform Censys shows that there are more than 40,000 internet-exposed industrial control systems (ICS) in the United States, and notifying their owners about the exposure is in many cases impossible.
Censys pointed out that more than half of these systems are likely associated with building control and automation, and roughly 18,000 are actually used to control industrial systems.
The company also found that more than half of the hosts running low-level automation protocols, which enable communications between ICS, are concentrated in wireless and consumer access networks such as Comcast and Verizon.
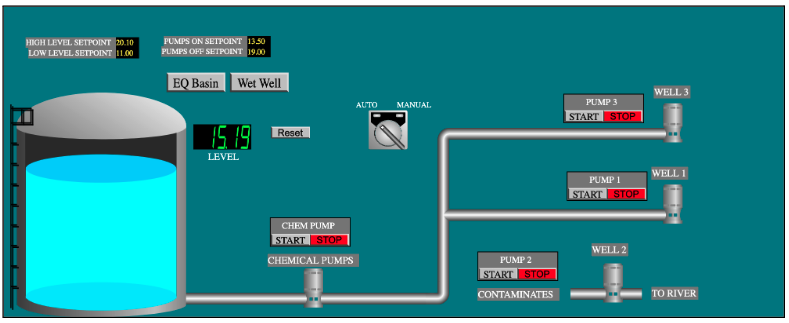
In the case of human-machine interfaces (HMIs), which are used to monitor and control industrial systems, 80% are in networks provided by companies such as AT&T and Verizon.
The fact that these systems are hosted on wireless or consumer networks means it’s likely not possible to contact the owner and warn them about the exposure.
“While HMIs and web administration interfaces occasionally offer clues as to ownership (e.g., city or location information in the user interface), automation protocols rarely expose such context, making it impossible to determine sector or organizational ownership for these devices. In turn, this makes notifying the owners of these device exposures impossible in many cases,” Censys explained.
In the case of HMIs associated with water systems, Censys found that nearly half can be manipulated without authentication.
The risks associated with these exposed HMIs are not only theoretical. Threat actors have been known to target such systems in their attacks.
A group of alleged hacktivists calling itself ‘Cyber Army of Russia Reborn’ caused a small Texas town’s water system to overflow.
The Cyber Av3ngers hacktivist group, which is believed to be a persona used by the Iranian government, has targeted multiple water facilities in the United States.
In addition, the China-linked Volt Typhoon group can also pose a serious threat to ICS and other operational technology (OT) systems, with evidence suggesting that they have been exfiltrating sensitive data.
| Learn More at SecurityWeek’s ICS Cybersecurity Conference The leading global conference series for Operations, Control Systems and OT/IT Security professionals to connect on SCADA, DCS PLC and field controller cybersecurity.  October 21-24, 2024 | Atlanta www.icscybersecurityconference.com |
Related: EPA Issues Alert After Finding Critical Vulnerabilities in Drinking Water Systems
Related: FrostyGoop ICS Malware Left Ukrainian City’s Residents Without Heating

