The cybersecurity agency CISA regularly updates its Known Exploited Vulnerabilities (KEV) catalog when it learns of a flaw being leveraged in ransomware attacks, but the practical utility of these updates for defenders has been questioned because they are made without public notification.
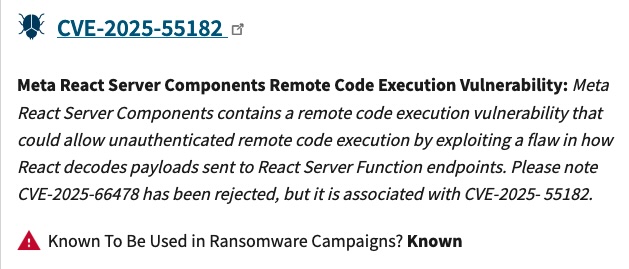
Since late 2023, each entry in CISA’s KEV catalog has indicated whether the vulnerability has been observed in ransomware campaigns, helping defenders prioritize patches.
According to Glenn Thorpe, senior director of security research and engineering at threat intelligence firm GreyNoise, CISA updated the entries for 59 vulnerabilities in 2025 to flip the ‘known to be used in ransomware campaigns’ data field from ‘unknown’ to ‘known’.
The fastest flip came after one day and the longest time-to-flip was more than 1,300 days.
Vulnerabilities in Microsoft products account for more than a quarter of the updated CISA KEV entries (16 CVEs), followed by Ivanti (6 CVEs), Fortinet (5 CVEs), Palo Alto Networks (3 CVEs), and Zimbra (3 CVEs).
The most common vulnerabilities for which CISA received reports of exploitation by ransomware groups were authentication bypass and remote code execution.
Thorpe described the KEV updates as representing a material change to an organization’s risk posture. “Your prioritization calculus should shift. But there’s no alert, no announcement. Just a field change in a JSON file,” the expert said.
“We’re good at reacting to new disclosures. Decent at tracking active exploitation. But we’re not great at noticing when the characterization of existing threats evolves,” Thorpe noted.
“CISA is already tracking these ransomware campaigns, correlating TTPs, and updating assessments. That intelligence only matters if defenders are watching the delta, not just the headlines,” he added.
Contacted by SecurityWeek, CISA Executive Assistant Director for Cybersecurity Nick Andersen said the agency aims to help defenders prioritize risk by including the ransomware tag in KEV entries.
“We continue to streamline processes and enrich vulnerability data through initiatives like the KEV catalog, the Common Vulnerabilities and Exposures (CVE) Program, and Vulnrichment,” Andersen said in an emailed statement. “Feedback from the cybersecurity community is essential as CISA works to enhance the KEV catalog and advance vulnerability prioritization across the ecosystem.”
Until CISA makes the KEV entry updates more transparent, GreyNoise’s Thorpe has created a simple tool: an RSS feed. By subscribing to the feed, which checks for updates every hour, organizations will be alerted whenever the value of a ransomware tag changes in CISA’s catalog.
Related: Fresh SolarWinds Vulnerability Exploited in Attacks
Related: Vulnerabilities in CISA KEV Are Not Equally Critical
Related: Exploitation Long Known for Most of CISA’s Latest KEV Additions
Related: CISA KEV Catalog Expanded 20% in 2025, Topping 1,480 Entries

