A ransomware attack targeting a third-party emergency alert system used across the United States has resulted in a data breach and significant disruptions.
Cities, counties, and law enforcement in many US states informed the public over the past week that the OnSolve CodeRED emergency alert system provided by Crisis24 has been disrupted due to a cyberattack, leaving them unable to send emergency notifications.
The CodeRED system is used for alerts triggered by public safety events such as floods, gas leaks, chemical spills, fires, missing persons, and bomb threats.
The incident did not impact the national Emergency Alert System (EAS).
Notifications related to the CodeRED cybersecurity incident have been posted by local government organizations in Massachusetts, Colorado, Texas, Florida, North Carolina, Ohio, Kansas, Georgia, California, Utah, Missouri, Montana, New Mexico, and other states.
Crisis24 does not appear to have issued a statement on the matter, but the notifications from its customers revealed that cybercriminals obtained OnSolve CodeRED user data such as names, email addresses, physical addresses, phone numbers, and user profile passwords associated with a legacy platform.
SecurityWeek has reached out to Crisis24 for comment.
Some customers are reportedly attempting to cancel CodeRED contracts due to the impact of the cybersecurity incident. Some of the affected local government agencies said they are transitioning to a new CodeRED platform after the vendor discontinued the legacy platform targeted by the hackers.
The Inc Ransom group, which recently also targeted the Pennsylvania Office of the Attorney General, is behind the OnSolve attack, listing it on its leak website on November 22.
The cybercriminals claimed to have gained access to OnSolve systems on November 1 and deployed file-encrypting ransomware on November 10. They suggested that negotiations failed after the vendor was only willing to pay a $100,000 ransom.
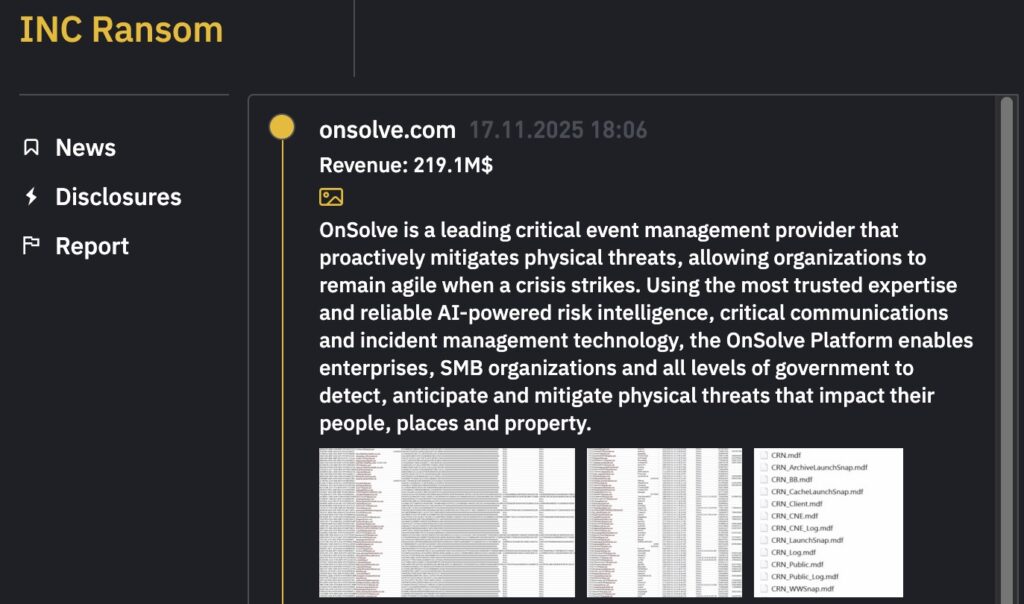
While the notifications issued by cities and counties state that the stolen data has not been published online, the cybercriminals have since made public some files allegedly stolen during the attack.
Inc Ransom said that it put the stolen data up for sale.
UPDATE: Crisis24 has provided the following statement to SecurityWeek:
We confirm that data potentially associated with the legacy OnSolve CodeRED platform has been published online following a targeted attack by an organized cybercriminal group. The attack also resulted in damage to the OnSolve CodeRED environment. Current forensic analysis indicates that the incident was contained within that environment, with no contagion beyond. We have notified law enforcement and the investigation is ongoing.
The dataset involved may include information for OnSolve CodeRED users. Users who have reused their OnSolve CodeRED password for any other personal or business accounts are advised to change those passwords immediately. We have notified all affected OnSolve CodeRED customers (cities, counties, states, etc) and have decommissioned the platform. In parallel, we have accelerated the rollout of our new CodeRED by Crisis24 platform and are transferring all customers to this platform for their alerting and notification needs.
Cyberattacks remain a persistent threat across all sectors, and we regret that this incident has occurred. We remain fully committed to supporting our customers and ensuring their basic alerting and public notification requirements continue to be met without interruption.
Related: Akira Ransomware Group Made $244 Million in Ransom Proceeds
Related: Dartmouth College Confirms Data Theft in Oracle Hack
Related: Synnovis Confirms Patient Information Stolen in Disruptive Ransomware Attack

