The Russia-linked Star Blizzard APT earlier this year targeted French press freedom organization Reporters Without Borders (RSF), Sekoia reports.
The attack occurred in March and was carried out via a phishing email targeting one of RSF’s core members.
Star Blizzard used a ProtonMail address and spoofed a recipient’s trusted contact, asking them to review an attached document. On purpose, the Russian hackers did not attach the document, and instead waited for the recipient to respond and ask for it, Sekoia notes.
The second email contained a link to a compromised website that redirected to a PDF hosted on ProtonDrive. However, the PDF file could not be retrieved, as Proton had blocked the operator’s account.
As part of the attack against Reporters Without Borders, the Star Blizzard APT sent phishing emails in both French and English and used peace negotiation themes to lure the intended victim into clicking on the malicious link.
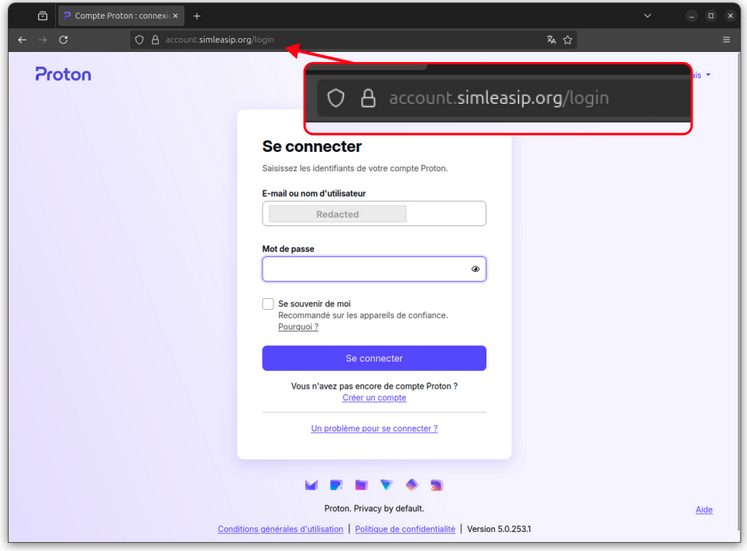
Star Blizzard’s phishing kit targets ProtonMail accounts
In a second attack involving a different organization, the threat actor attached a ZIP archive posing as a PDF file to its phishing email.
The file displayed a message claiming the document was encrypted, luring the victim into clicking a link to a compromised website that redirected to a phishing kit.
According to Sekoia, the kit was designed to target ProtonMail accounts and can relay two-factor authentication.
Likely homemade, the kit allows the APT to inject malicious JavaScript into the victim’s sign-in page, using an adversary-in-the-middle (AiTM) technique.
The modified sign-in page has the username pre-filled and keeps the victim’s cursor focused on the password field.
More complex code injected into the page interacts with an attacker-controlled API that processes the credentials and acts as an intermediary between the user and the legitimate ProtonMail authentication interface.
The fresh attacks, Sekoia says, are a continuation of Star Blizzard’s spear-phishing campaigns that employ the ClickFix technique.
“If you are an NGO involved in Ukraine, or an individual or researcher with intelligence on this conflict and partnering with Ukrainian bodies, you are possibly one of the targets of this threat actor,” Sekoia notes.
Also tracked as UNC4057, Callisto, ColdRiver, and Seaborgium, the Star Blizzard APT has been active since at least 2019, targeting government entities, academic organizations, NGOs, and think tanks.
In 2023, the US government publicly linked the hacking group to Russia’s Federal Security Service (FSB). Earlier this year, it was seen using the LostKeys malware in attacks against government and military advisors, journalists, think tanks, and non-profits.
Related: Russian APT Switches to New Backdoor After Malware Exposed by Researchers
Related: Russian Government Hackers Caught Buying Passwords from Cybercriminals
Related: US and Allies Sanction Russian Bulletproof Hosting Service Providers
Related: Destructive Russian Cyberattacks on Ukraine Expand to Grain Sector

