Meta has started addressing WhatsApp vulnerabilities that expose user metadata, specifically targeting flaws that allow adversaries to ‘fingerprint’ a device’s operating system. However, fully masking these signatures is an ongoing challenge.
When threat actors want to deliver sophisticated spyware to a user, they may pick WhatsApp, which has 3 billion users, as a delivery channel. To achieve their goal, the attackers can exploit zero-day vulnerabilities that enable them to deliver a malicious payload to WhatsApp users without any interaction from the victim.
These zero-days can impact WhatsApp itself and third-party components that enable the delivery of spyware through other applications that rely on these components. Paragon spyware attacks that came to light in 2025 targeted dozens of users through the exploitation of such flaws.
WhatsApp zero-days are rare and highly valuable to both attackers and defenders, with $1 million regularly offered by both sides for full-chain exploits.
Device fingerprinting
However, before attackers can exploit WhatsApp zero-days to deliver their malicious payloads, they need to determine the targeted user’s operating system to push the appropriate type of payload.
This can be achieved in the reconnaissance phase of the attack. Researchers have shown over the past two years that an attacker only needs the targeted user’s phone number to collect information about their devices and operating systems. The process requires no user interaction and leaves the victim with no indication that their information has been harvested.
Researchers demonstrated how an attacker can infer the user’s primary device, the operating system of each linked device, the devices’ age, and whether WhatsApp is running through a mobile app or a web browser on a desktop device. This can be determined due to the predictable values of encryption key IDs assigned by the messaging application.
One of the individuals spearheading these investigations is Tal Be’ery, a reputable researcher and co-founder and CTO of the Zengo cryptocurrency wallet.
Be’ery and others have reported their findings to Meta, but the internet giant did not appear to take any action, until recently.
Be’ery has developed a tool for WhatsApp device fingerprinting. The tool is not public, but it recently showed the researcher that Meta has started taking some steps to prevent device fingerprinting by assigning random values to key IDs, specifically for Android devices.
The researcher, who described the findings in a blog post published on Monday, has demonstrated for SecurityWeek that the device fingerprinting technique still works. However, he applauded Meta for recognizing it as a security and privacy issue and taking steps to address it.
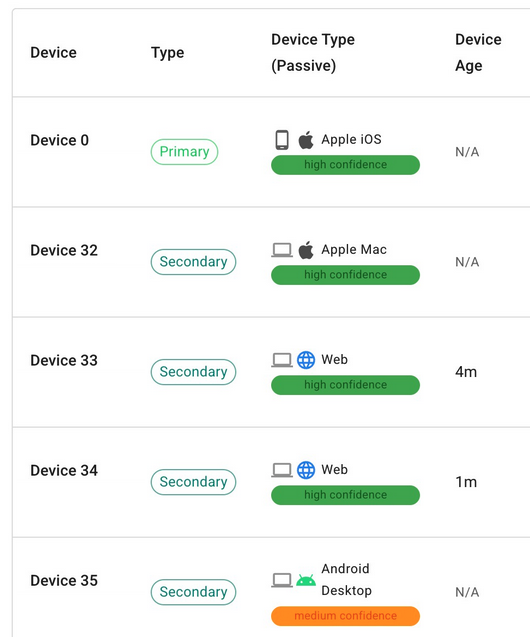
“Attackers can still distinguish with high certainty between Android and iPhone based on One-Time PK ID,” Be’ery explained. “Since iPhone initializes this parameter with a low value and slowly increments it (every few days), it is still highly distinguishable from Android’s random value, which makes use of its entire 24-bit potential.”
“However, it seems reasonable to believe that this is WhatsApp’s first step toward a more complete fix that will make these fields random on all operating systems and platforms. If indeed this is the plan, it will obliterate this fingerprinting privacy vulnerability,” he added.
While he believes Meta has taken steps in the right direction, the researcher criticized the ‘silent’ nature of the rollout, noting that WhatsApp users remain unaware of the underlying changes. He also believes Meta should do a better job communicating with researchers who report these types of issues, assign CVE identifiers, and pay bug bounties.
Response from WhatsApp
WhatsApp told SecurityWeek that it remains focused on protecting users against many different attack vectors while still ensuring it can smoothly run its popular messaging service.
WhatsApp has confirmed that it has been taking steps to harden its application, including against device fingerprinting.
However, it pointed out several aspects regarding OS inference and why these issues are typically considered low severity:
- Device fingerprinting is not limited to WhatsApp and can be done through many technologies and platforms.
- Operating systems themselves can make device fingerprinting trivial to enable a better user experience (for example, typing in a number on iMessage to see if someone is on Apple OS or Android, without sending any message).
- Inferring device OS stems from the differences in how varying operating systems function, requiring developers to build app versions tailored for each one in order to optimize their performance for the user.
- OS inference has a limited practical security impact. It has marginal utility without a zero-day that could allow an attacker to deliver malicious code aimed at a particular OS.
- The cybersecurity industry typically rates the severity of OS fingerprinting (both active and passive inference) as low severity, and these types of issues rarely meet the severity threshold for a CVE. The issues reported by Be’ery did not meet WhatsApp’s threshold.
Nevertheless, WhatsApp says Be’ery’s report did help the company address a separate but similar issue in the handling of invalid messages, as well as to improve its bug bounty triage process in this area. The researcher has been awarded a bug bounty for this contribution.
Meta has paid out $25 million through its bug bounty program since its inception, including $4 million in 2025.
In the case of WhatsApp specifically, Meta says it has been making improvements to security, including through a WhatsApp Research Proxy tool that makes research into WhatsApp’s network protocol more effective.
As for its fight against spyware, Meta has been taking action on several fronts, including disrupting operations aimed at its applications, sharing its findings with industry peers and researchers to help them detect such activity, raising awareness among users, and filing lawsuits against spyware makers.
Meta last year won a lawsuit against spyware firm NSO Group. NSO has been ordered to stop hacking WhatsApp and pay millions in punitive damages, but the spyware maker has filed an appeal.
Related: Vulnerability Allowed Scraping of 3.5 Billion WhatsApp Accounts
Related: CISA Warns of Spyware Targeting Messaging App Users
Related: Landfall Android Spyware Targeted Samsung Phones via Zero-Day

