The Open Web Application Security Project (OWASP) has released a revised version of its Top 10 list of critical risks to web applications, adding two new categories and reshuffling the overall list order.
This 2025 release candidate, which is a near-final draft of the flagship OWASP Top 10 list, is open for comment until November 20.
Broken Access Control has maintained the leading position on the 2025 OWASP Top 10 list, after climbing there in 2021. The Broken Access Control category now incorporates server-side request forgery (SSRF), which was previously separate and tenth on the list.
Security Misconfiguration is now second on the list, up from fifth in the 2021 OWASP Top 10, followed by Software Supply Chain Failures, an expansion of Vulnerable and Outdated Components, which was previously sixth.
The expanded category includes “a broader scope of compromises occurring within or across the entire ecosystem of software dependencies, build systems, and distribution infrastructure,” OWASP notes, pointing out that it emerged as a top concern in the community survey.
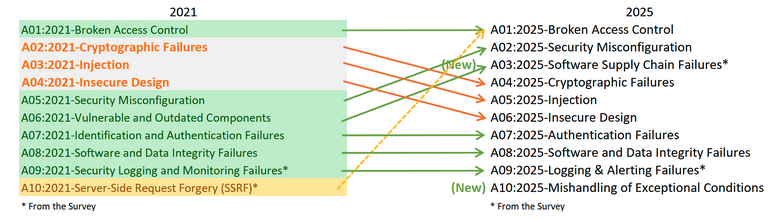
The Cryptographic Failures, Injection (which includes XSS and SQL Injection), and Insecure Design categories each dropped two places and are now in fourth, fifth, and sixth positions, respectively.
Authentication Failures, Software or Data Integrity Failures, and Logging & Alerting Failures maintained the seventh, eighth, and ninth spots they had on the 2021 OWASP Top 10.
New to the list is the Mishandling of Exceptional Conditions category, now on tenth place. It includes failing open, improper error handling, logical errors, and other scenarios associated with abnormal conditions systems may encounter.
According to OWASP, some of the categories in this installment of the list have been changed compared to 2021, mainly due to a slightly different approach.
“In this iteration, we asked for data, with no restriction on CWEs like we did for the 2021 edition. We asked for the number of applications tested for a given year (starting in 2021), and the number of applications with at least one instance of a CWE found in testing. This format allows us to track how prevalent each CWE is within the population of applications,” OWASP explains.
The organization focused on the root cause and ignored the frequency of a CWE within the same application, and used a pool of 589 CWEs for analysis, compared to 30 CWEs in 2017 and nearly 400 CWEs in 2021.
“We plan to do additional data analysis as a supplement in the future. This significant increase in the number of CWEs necessitates changes to how the categories are structured,” OWASP notes.
However, the team used CVE data for Exploitability and (Technical) Impact, and calculated average exploit and impact scores by grouping CVEs with CVSS scores by CWE and looking at the percentage of applications that had CVSSv3 and CVSSv2 scores.
Due to the limits of automated testing, only eight categories have been selected from this data, which is considered incomplete. The other two categories come from the Top 10 community survey, in which practitioners vote for what they consider the highest risks.
Related: MITRE Unveils ATT&CK v18 With Updates to Detections, Mobile, ICS
Related: MITRE Unveils AADAPT Framework to Tackle Cryptocurrency Threats
Related: MITRE Updates List of Most Common Hardware Weaknesses
Related: MITRE Updates List of 25 Most Dangerous Software Vulnerabilities

