A fresh variant of the ClickFix attack relies on a malicious Chrome extension to display a security warning and lure victims into executing unwanted commands to install malware, Huntress reports.
Dubbed CrashFix, the attack starts with the NexShield browser extension, which impersonates the legitimate uBlock Origin Lite ad blocker.
The extension displays a fake security warning instructing the victim to fix allegedly identified issues by opening the Windows Run dialogue and pasting content from the clipboard.
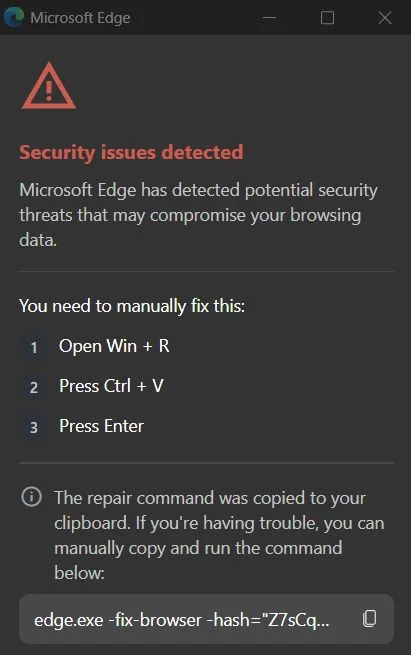
Just as in the classic ClickFix attacks, NexShield silently copies malicious PowerShell commands to the clipboard, masquerading as a repair command, designed to infect the victim’s system with ModeloRAT.
However, only hosts that are domain-joined are infected, which suggests that the threat actor behind the campaign, dubbed KongTuke and active since at least early 2025, is targeting corporate environments.
The core malicious functionality of NexShield, Huntress explains, is a denial-of-service (DoS) attack against the victim’s browser, setting the stage for the CrashFix social engineering technique.
The extension executes a function that attempts to iterate 1 billion times, creating a chrome.runtime port connection with each iteration. Once it completes the iterations, it starts again, in an infinite loop.
This exhausts system resources and causes the browser to become unresponsive and crash. If the browser is restarted, the fake security warning triggering the CrashFix attack is displayed.
To avoid raising user suspicion, NexShield sets a timer so that the malicious behavior is triggered 60 minutes after installation. The DoS attack begins 10 minutes later and is executed every 10 minutes, but only against users for whom the extension has sent a user ID to the command-and-control (C&C) server.
A focus on enterprise environments
The malicious command that victims run in a CrashFix attack leads to the execution of the legitimate Windows utility Finger.exe, which can retrieve information about users on remote systems.
The command also retrieves a secondary payload that fetches and executes malicious code from a remote server, installing the fully-featured Python-based ModeloRAT remote access trojan on domain-joined systems.
The RAT performs system reconnaissance, establishes persistence, and supports command execution. It also features adaptive C&C beaconing, obfuscation, two-layered encryption, and anti-analysis capabilities.
According to Huntress, the malware operator appears focused on compromising corporate environments to gain access to Active Directory, internal resources, and sensitive data. Thus, ModeloRAT is not served to home users (an infection mechanism for hosts that are not domain-joined has not been implemented in CrashFix).
“KongTuke’s CrashFix campaign demonstrates how threat actors continue to evolve their social engineering tactics. By impersonating a trusted open-source project (uBlock Origin Lite), crashing the user’s browser on purpose, and then offering a fake fix, they have built a self-sustaining infection loop that preys on user frustration,” Huntress notes.
Related: Sophisticated ClickFix Campaign Targeting Hospitality Sector
Related: ClickFix Attacks Against macOS Users Evolving
Related: Chrome Extensions With 900,000 Downloads Caught Stealing AI Chats
Related: Chrome, Edge Extensions Caught Tracking Users, Creating Backdoors

