A newly identified Android remote access trojan (RAT) includes a one-click APK builder to wrap its payload inside legitimate applications, mobile security firm iVerify reports.
Dubbed Cellik, the RAT provides attackers with full control over the infected devices, and includes real-time surveillance capabilities like those found in advanced spyware.
These include screen streaming in real time, keylogging, remote access to camera and microphone, notification interception, a system for stealing data from other applications, and hidden browsing.
Once installed on a device, the Cellik Android RAT allows attackers to remotely control the UI, and to simulate taps or swipes.
Furthermore, it allows operators to browse through files, delete data, download or upload files, and access cloud storage services linked to the phone.
The malware comes with a hidden browser module that runs invisibly on the device, enabling attackers to navigate remotely to websites, click on links, and fill out forms, all while the attacker receives a stream of screenshots in real time.
“Using the hidden browser, a cybercriminal could quietly log into websites using the victim’s saved cookies, or auto-fill credentials on phishing pages. Cellik can capture any form data submitted in the hidden browser, so if the victim is tricked into entering passwords or credit card info, the RAT will intercept those details,” iVerify says.
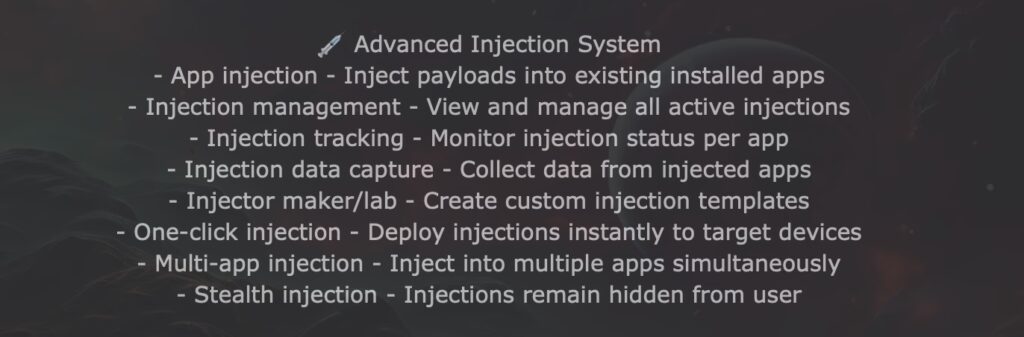
Cellik can also display overlays on top of other applications, such as fake login screens that intercept credentials. It comes with an injector lab for building custom injections targeting different applications, and supports multiple simultaneous injections across applications.
According to iVerify, the Cellik Android RAT also features Google Play integration, enabling attackers to browse the application catalog and select legitimate apps to bundle with the malicious payload.
Using the RAT’s built-in toolkit, threat actors can bundle applications with the Cellik payload remotely, with a single click.
“This means a cybercriminal can take a popular app (like a game or utility that targets are likely to install), insert Cellik’s code into it, and repackage it as an installer, all using Cellik’s built-in toolkit,” iVerify notes.
Cellik is being offered on the dark web at $150 per month. A one-month subscription with RDP costs $200, while a lifetime subscription is $900.
“What sets Cellik apart is its Play Store app integration and the sheer breadth of its capabilities for the price point. Those features include advanced location tracking, real-time multimedia capture, communications surveillance, crypto-wallet theft, and even AI driven analysis of user behavior,” iVerify notes.
Related: New Albiriox Android Malware Developed by Russian Cybercriminals
Related: Landfall Android Spyware Targeted Samsung Phones via Zero-Day
Related: Anatsa Android Banking Trojan Now Targeting 830 Financial Apps
Related: Undetectable Android Spyware Backfires, Leaks 62,000 User Logins

